Windows 10 Feature Updates can be tricky to troubleshoot. The trick is to find relevant information about what’s causing the Windows 10 Feature Update to fail.
In a previous post, we covered the Windows 10 Feature update error 0XC1900208. This is still accurate and possible that it happens for a Feature Update to Windows 10 20h2. We followed the instruction in the blog post to find what’s preventing the Feature Update to run.
We start to test the Feature Updates from Windows 10 1809 to 20h2 at a client site. Our previous post was not helping, since running Setup.exe manually returned a restart error.
We restarted the machine without success. This was not the problem.
In this blog post, we’ll describe how to troubleshoot Windows 10 Update hard blocks using various methods.
Troubleshoot Windows 10 Update hard block
The first place to look is in the Windows Panther folder:
- Browse to C:\$WINDOWS.~BT\Sources\Panther and look for CompatData files.
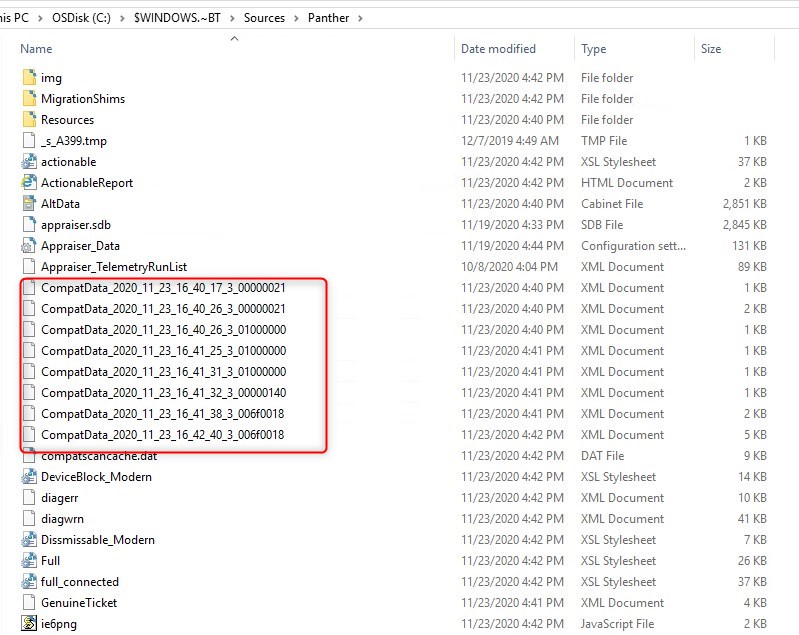
- Open up the CompatData file having the most recent date with a browser, since those are XML, it’s easier to read.
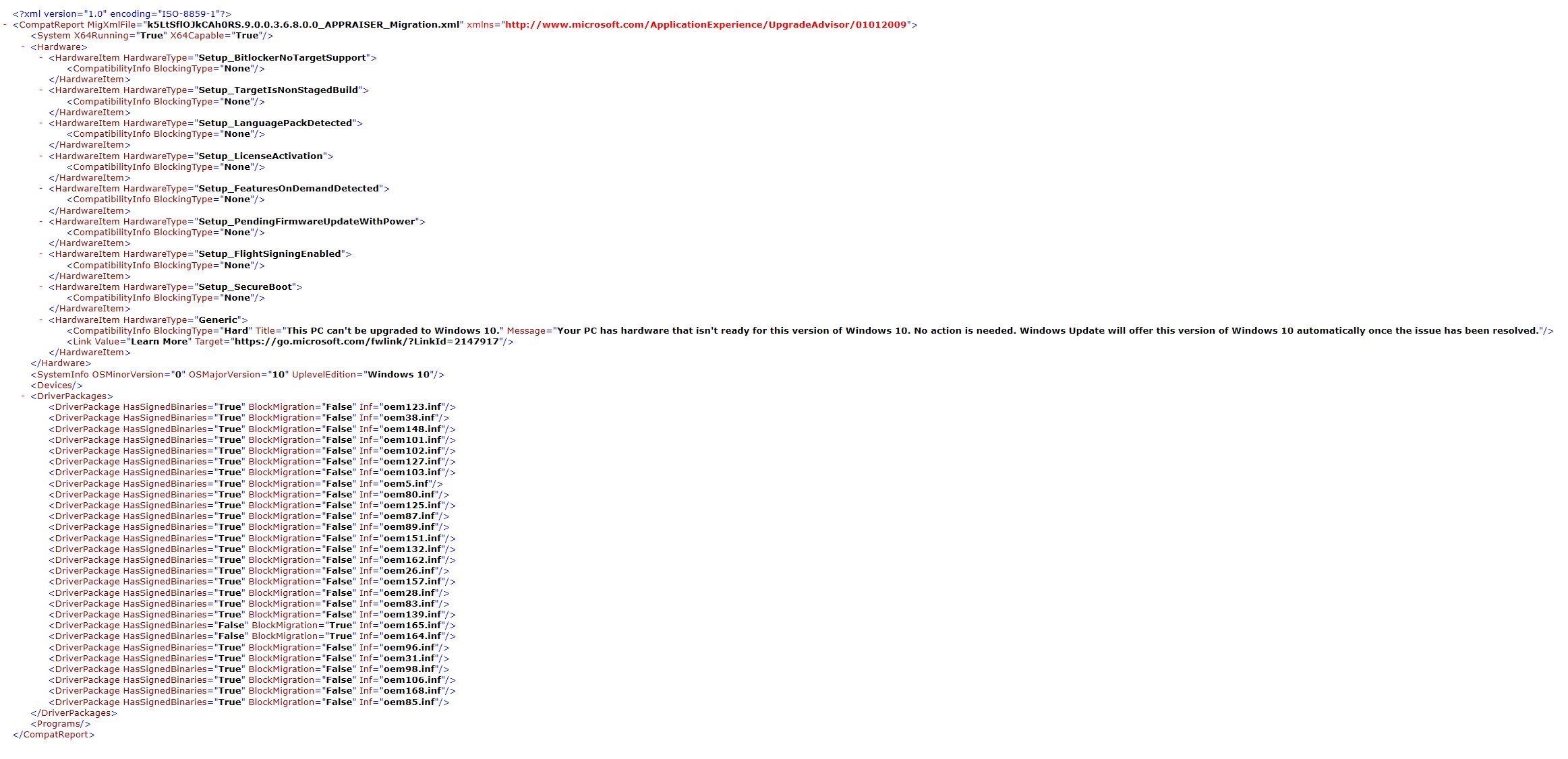
- Look for any BlockingType=Hard
- In this particular case, the result isn’t exactly clear on what is preventing this Windows 10 20h2 Feature Update to happen. I didn’t have a lot of fate via the Learn More Microsoft link, but to my surprise, it ended up being spot on!
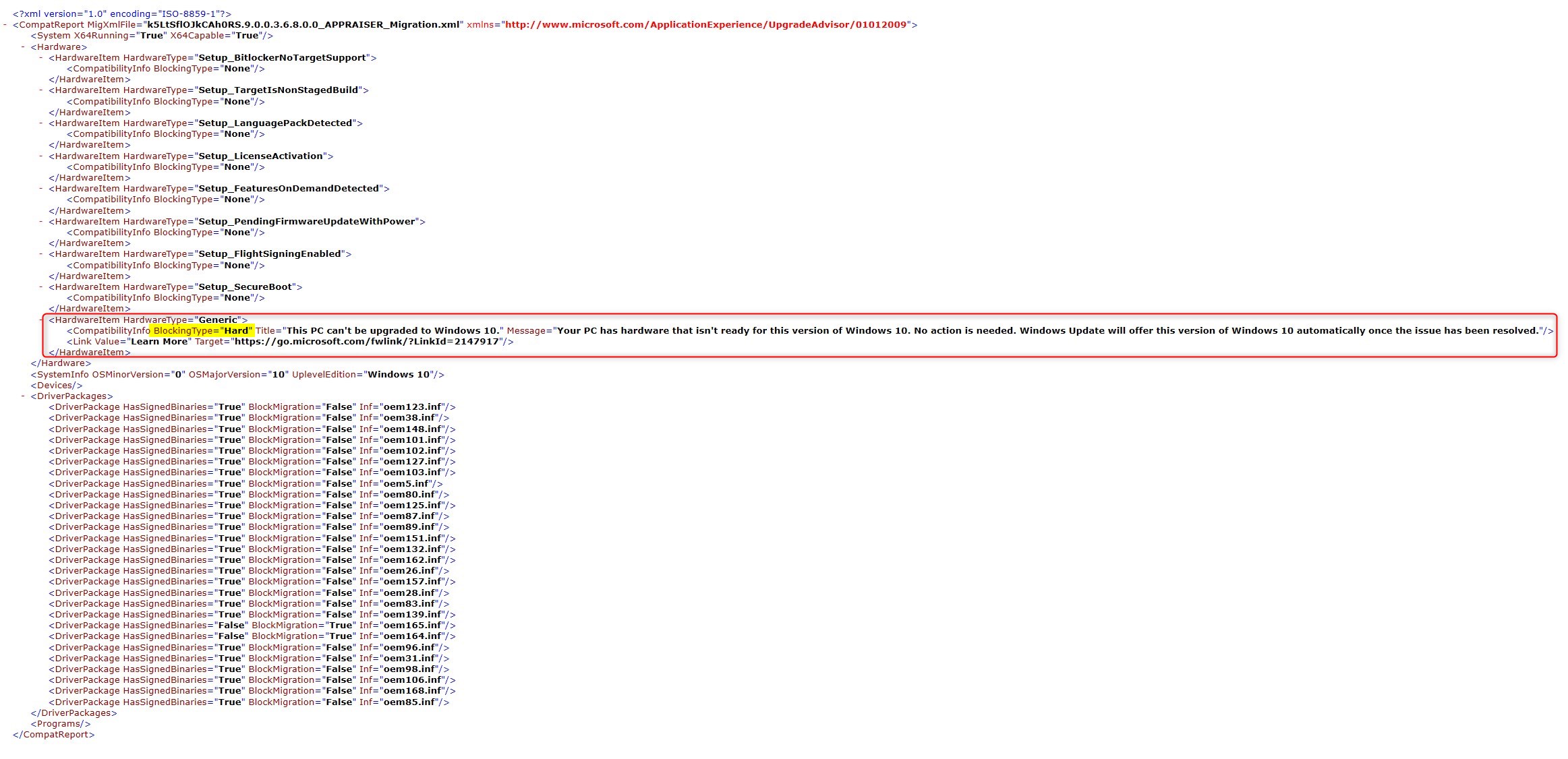
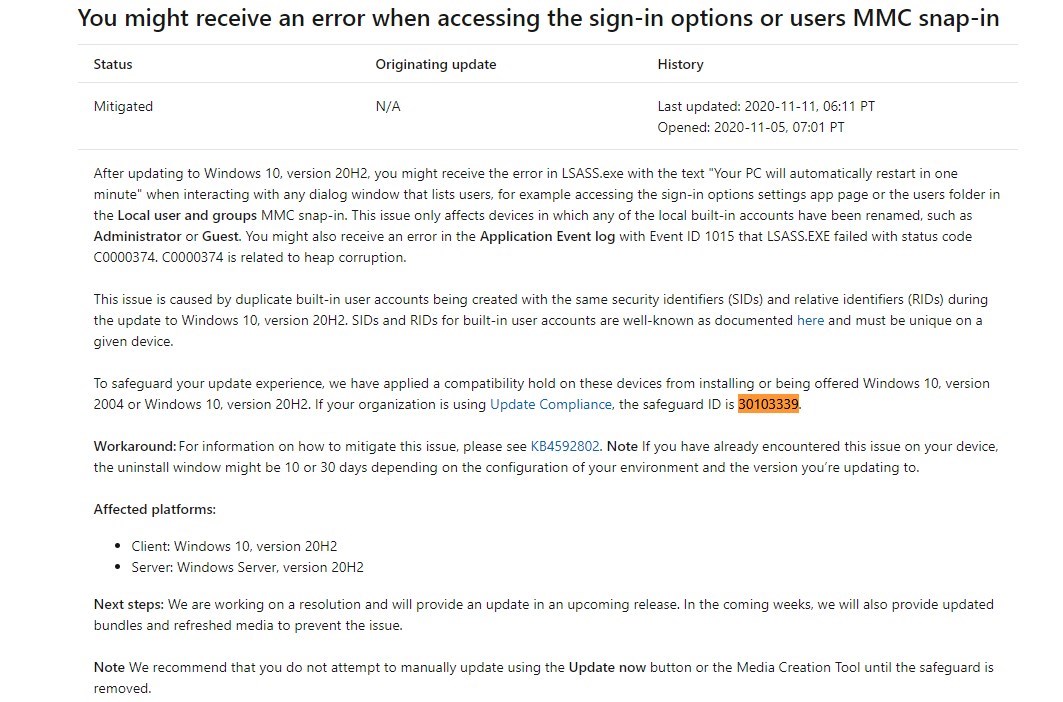
- This article was released about a month ago. For more details, see the full KB release
This issue is caused by duplicate built-in user accounts being created with the same security identifiers (SIDs) and relative identifiers (RIDs) during the update to Windows 10, version 20H2. SIDs and RIDs for built-in user accounts are well-known as documented here and must be unique on a given device.
- End result, changing the local administrator account back to its default name as described in the article resolved the Windows 10 feature Update error
Other methods to research hard blocks
With the precious help of fellow SCD Adam Gross, here are other ways to reach and find what is going on with some Windows 10 hard blocks.
Hard blocks are also known as SafeGuard. A feature to avoid installing feature updates while some key component on a system would break Windows 10 in a way or another.
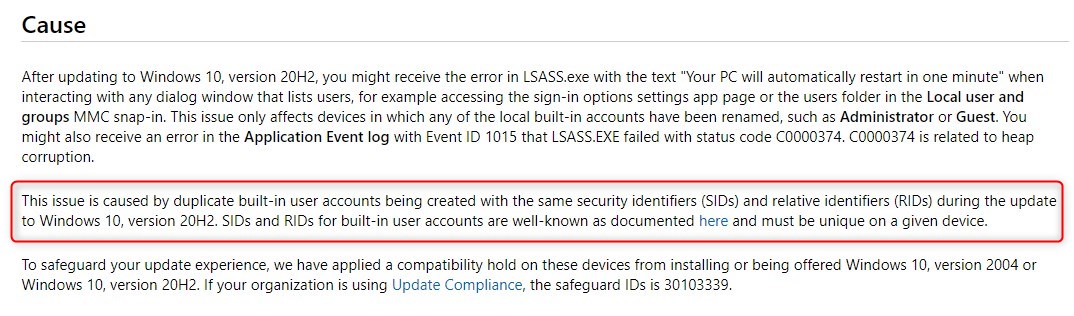
On the device that failed to run the Feature Update, those can be found in the registry under :
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\TargetVersionUpgradeExperienceIndicators\20H1.
They are referred to as GatedBlockID.
Finding GatedBlockID meaning
Each number in that registry key refers to a specific problem. Those are centralized under the known issues of the Windows 10 release.
Searching this page with the GatedBlockID code will lead to the description of the problem. In our case, we look for 30103339
CMPivot query to return GatedBlockIDs
Again, thanks to Adam Gross, here’s the CMPivot Query to find the GatedBlockID value.
Registry('HKLM:\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\AppCompatFlags\\TargetVersionUpgradeExperienceIndicators\\*\\') | where Property == 'GatedBlockId' and Value != 'None'With that said, this could be easily added to the hardware inventory of your SCCM clients. If so, collections could be created with various remediation to automate as much as possible the Windows 10 Feature Update process.
Adam shared a powershell script to help sorting why Windows 10 Feature Updates fail.
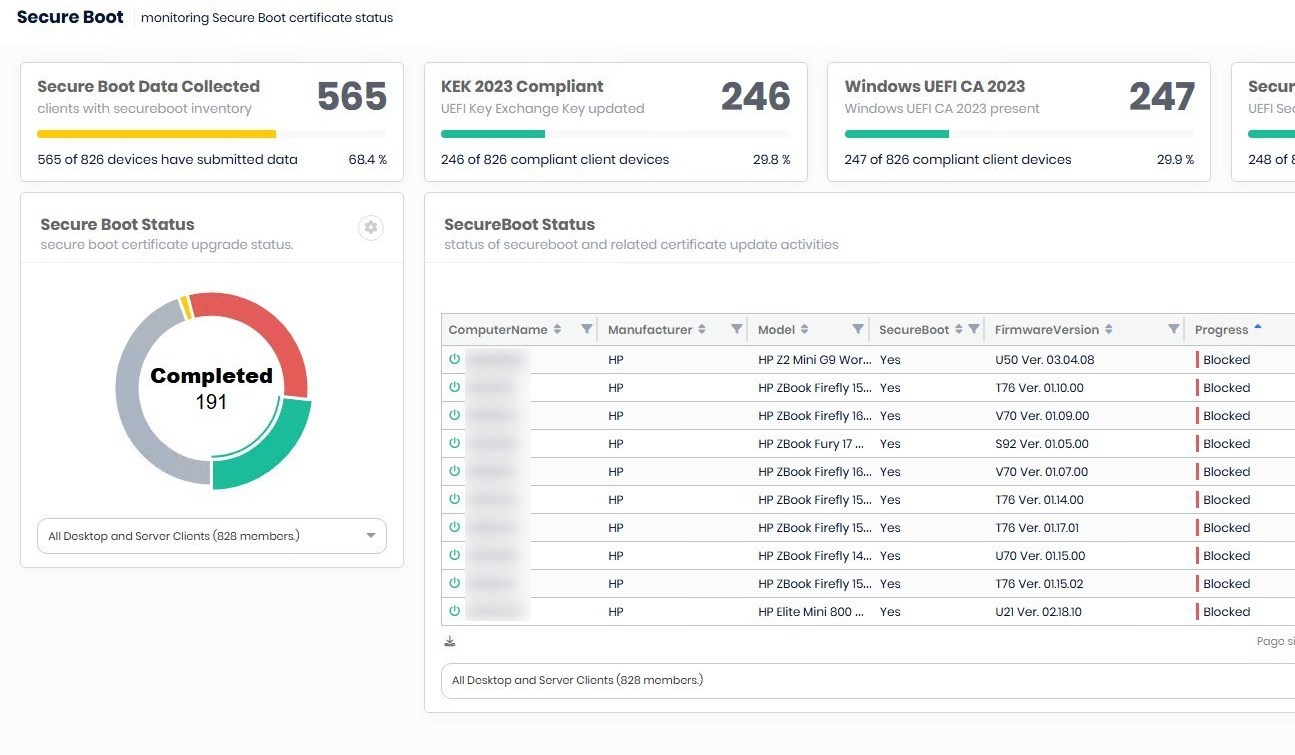
SafeGuard in Log Analytics Update Compliance
Even if your Windows 10 Updates are managed by MEMCM/ConfigMgr/SCCM, you can use Log Analytics Update Compliance to provide solid intel.
If you’re not using Update compliance, follow the Microsoft article to get started.
- Once Update Compliance has been added to your workspace, there’s a build-in query that lists devices with safeguard hold. Simply run the query Devices with a safeguard hold.
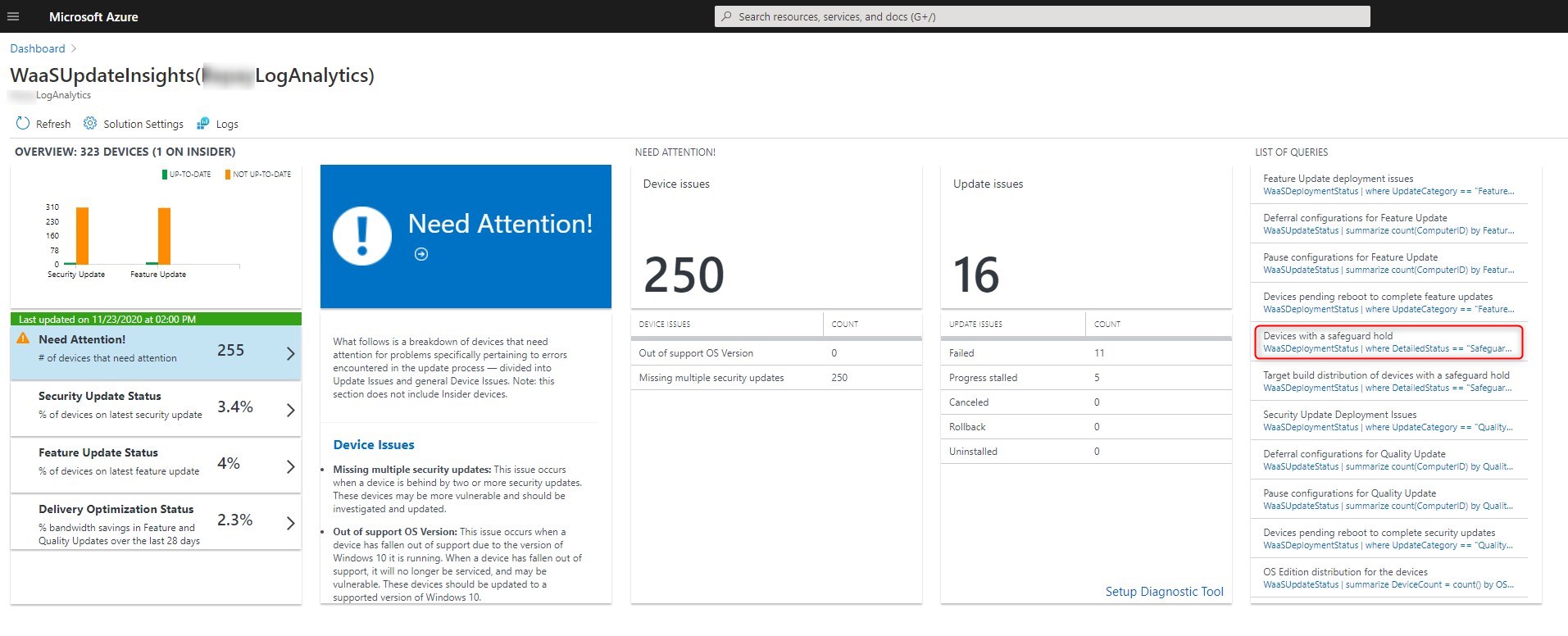
- The same information is returned as the CMPivot seen earlier.
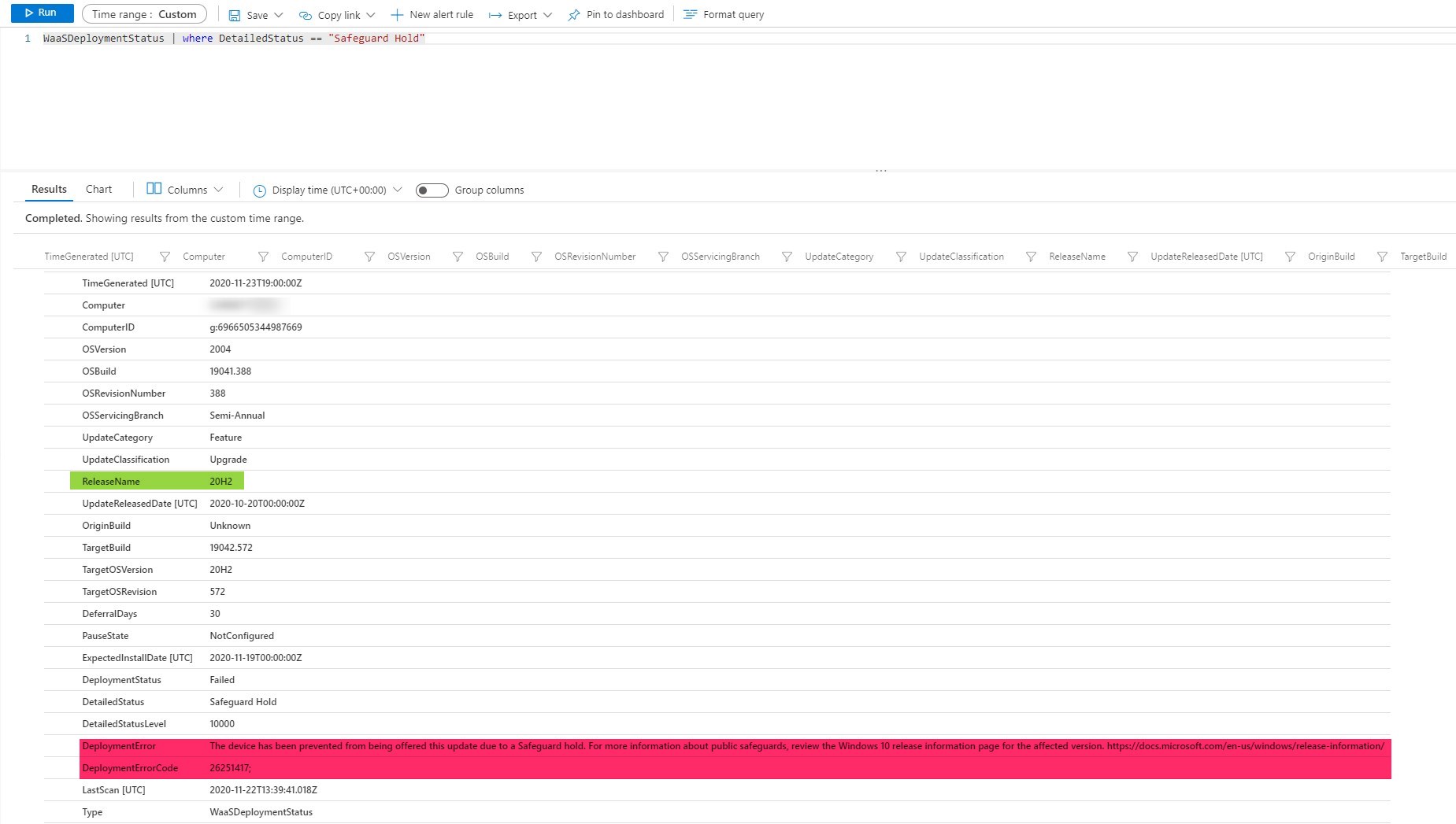
Follow this Microsoft article for more details about Update Compliance for Windows 10 Hard Block.
We hope that this post helps understand Windows 10 Update hard block.














Only authorized users can leave comments
Log In